Joomla! 1.5.6 e-Commerce Edition VM 1.1.2 LaiThai
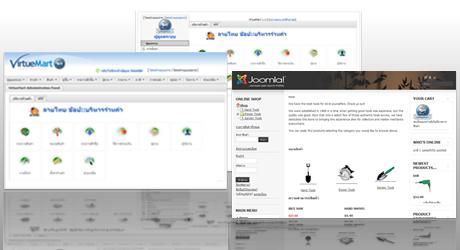
Joomla! 1.5.6 e-Commerce Edition VM 1.1.2 LaiThai เปิดตัวแล้วครับ สำหรับผู้ที่ต้องการใช้งานจูมล่าลายไทย 1.5.x ที่รวมร้านค้าออนไลน์ไว้แล้ว โดยมีการแสดงผลเป็นภาษาไทย พัฒนาจาก VirtueMart e-Commerce v1.1.2 และได้ทำการแก้ไขหลายๆ ส่วนด้วยกัน ดังนี้
- เพิ่มชื่อจังหวัด พร้อมตัวย่อเป็นภาษาไทยไว้ในฐานข้อมูลให้ โดยไม่ต้องไปเพิ่มเอง
- แก้ไขการแสดงวันที่หลายตำแหน่ง ให้เป็นภาษาไทย และอ่านออกได้ในแบบ UTF-8
- แก้ไขการแสดงผลของข้อคิดเห็น (Comment) ให้แสดง และตัดคำในการแสดงผลได้ถูกต้อง
- แก้ไขการแสดงผลของรายการในเทมเพลต จากตัวเอียง เป็นตัวปกติ
ซึ่งรายละเอียดของไฟล์ที่ได้ทำการแก้ไขไปแล้วนั้น จะอยู่ใน zip package ครับ ชื่อไฟล์ VirtueMart_1.1.2 eCommerce Bundle Joomla! 1.5.6 Log File.txt หากต้องการทราบก็เปิดอ่านได้ครับ
 ประกาศถึงสมาชิกที่ใช้งาน Joomla! อยู่ในขณะนี้ ตอนนี้ได้มีเวอร์ชันใหม่คือ Joomla! 1.5.6 [ Vusani ]. ซึ่งเวอร์ชันนี้ ได้ถูกประกาศต่อจากเวอร์ชันที่แล้วอย่างรวดเร็ว เพื่อแจ้งให้ทราบถึงการแก้ไขตำแหน่งที่ไม่ปลอดภัยระดับสูงที่เกิดขึ้น โดยแนะนำให้ผู้ใช้งานเวอร์ชันเก่า อัพเกรดโดยทันที
ประกาศถึงสมาชิกที่ใช้งาน Joomla! อยู่ในขณะนี้ ตอนนี้ได้มีเวอร์ชันใหม่คือ Joomla! 1.5.6 [ Vusani ]. ซึ่งเวอร์ชันนี้ ได้ถูกประกาศต่อจากเวอร์ชันที่แล้วอย่างรวดเร็ว เพื่อแจ้งให้ทราบถึงการแก้ไขตำแหน่งที่ไม่ปลอดภัยระดับสูงที่เกิดขึ้น โดยแนะนำให้ผู้ใช้งานเวอร์ชันเก่า อัพเกรดโดยทันที ทีมจูมล่าลายไทย ได้รีลีสต์ไฟล์ภาษาสำหรับใช้งานบนจูมล่า 1.5.5 แล้ว ซึ่งในแพคเกจของไฟล์ภาษา ได้ถูกสร้างออกมา 3 รูปแบบ ดังนี้
ทีมจูมล่าลายไทย ได้รีลีสต์ไฟล์ภาษาสำหรับใช้งานบนจูมล่า 1.5.5 แล้ว ซึ่งในแพคเกจของไฟล์ภาษา ได้ถูกสร้างออกมา 3 รูปแบบ ดังนี้ Joomla! community มีความยินดีที่จะประกาศเปิดตัว Joomla! 1.5.5 [Mamni] ซึ่งรีลีสนี้เป็นการปรับปรุงแก้ไขเร่งด่วนเรื่อง
Joomla! community มีความยินดีที่จะประกาศเปิดตัว Joomla! 1.5.5 [Mamni] ซึ่งรีลีสนี้เป็นการปรับปรุงแก้ไขเร่งด่วนเรื่อง