Joomla 1.7.4 ออกแล้ว
 ทีม Joomla! Project ได้ปล่อย Joomla 1.7.4 ออกมาให้ได้ใช้งานเป็นการเร่งด่วน ซึ่งมีการแก้ไขเกี่ยวกับเรื่องความปลอดภัย
ทีม Joomla! Project ได้ปล่อย Joomla 1.7.4 ออกมาให้ได้ใช้งานเป็นการเร่งด่วน ซึ่งมีการแก้ไขเกี่ยวกับเรื่องความปลอดภัย
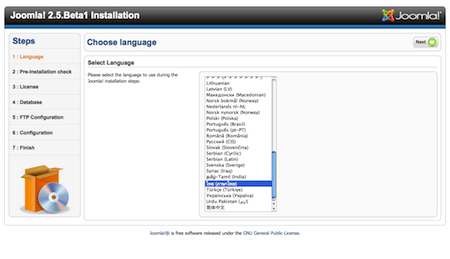
โปรดทราบว่า ผู้ใช้ส่วนใหญ่ควรจะปรับปรุงเว็บไซต์ของตนเอง เพื่อให้เป็นเวอร์ชัน 2.5.0 แทนของเดิม ซึ่งถูกปล่อยออกมาแล้วในขณะนี้ เวอร์ชัน 1.7.4 มีไว้สำหรับผู้ใช้ที่มีเหตุผลบางอย่าง ที่ไม่สามารถที่จะปรับปรุงให้เป็นเวอร์ชัน 2.5.0 ได้ ส่วนเวอร์ชั่น 1.7 จะมีระยะเวลาของการให้บริการจนถึงวันที่ 24 กุมภาพันธ์ 2555
เป้าหมายที่ยิ่งใหญ่ของทีมผ่ายผลิต คือการให้ความช่วยเหลือต่อไปอย่างสม่ำเสมอ เพื่อชุมชน Joomla. ท่านสามารถเรียนรู้เพิ่มเติมเกี่ยวกับ Joomla! Developement ที่เว็บไซต์นักพัฒนา.
ถ้าคุณกำลังต้องการที่จะอัพเกรดเว็บไซต์ของคุณ ที่ใช้เวอร์ชัน 1.7 อยู่ คุณควรจะทราบถึงวิธีการของการอัพเกรด ที่มีการเปลี่ยนแปลงตั้งแต่ Joomla 1.5 มา ดังนั้นเราจึงขอแนะนำให้คุณดูในหัวข้อ คำแนะนำ ด้านล่างนี้